Higher Highs and Higher Lows: The Market’s Way of Whispering “Win”
Aug 8, 2025
Price doesn’t just move—it accumulates memory. Every swing carves psychological sediment into the tape. What looks like motion is really momentum’s echo—conviction colliding with doubt, over and over, until structure forms.
Higher highs and higher lows aren’t trends. They’re behavioural scaffolding. Proof that bias didn’t just flare—it held. That fear blinked, and the crowd leaned in. That buyers didn’t just act—they anchored.
Think in vectors, not candles.
HL → HH is not a pattern—it’s power compounding across timeframes.
LL → HL is not recovery—it’s the first breath after collapse.
This isn’t price action. This is the market reprogramming its own nervous system.
Each HL is a pressure valve. Each HH is a breakout in belief.
Stack them, and what you get isn’t a trend. It’s a vote of confidence mutating into inevitability.
Want to see who survives? Track who adapts when the structure flips.
Let’s step into the rhythm beneath the surface.
Let’s time-travel.
Back to 1996: The SPX in Dialogue With Itself
Pull up a monthly SPX chart from 1996. Zoom out far enough, and the noise melts into rhythm. Zoom in just enough, and you catch the whisper of structure.
This isn’t just a ride up. It’s a drama in acts: dot-com delusion, GFC detonation, pandemic panic. But through every collapse, there’s a subtle pulse: HL → LL → HL. Or LL → LL → HL → HL. These are not just price actions. They’re psychological recurrences—traces of collective sentiment. Artefacts of belief.
Before we chart the history, let’s become familiar with the structure.
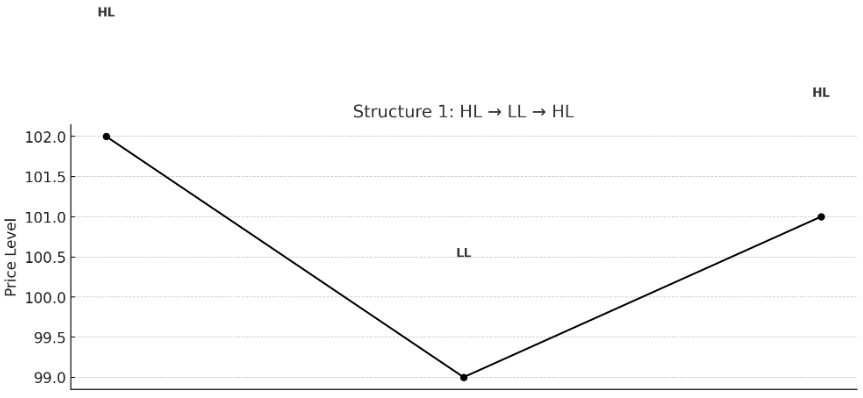
HL → LL → HL: The Flush & Recovery
The first HL is a tease—a wink. The market tries to bottom. It fails.
Then the LL hits. The panic moment. The stopper. The VIX-spiker. That’s when you hear the phrase: “market in free fall.”
But then comes the second HL. No new low. Just a higher base. That’s the shift. That’s where the smart money stops shorting and starts planning.
Thinkers Enter Stage Left:
- Laozi would’ve called this the “yielding that overcomes the strong.” Soft higher lows breaking the hard narrative of decline.
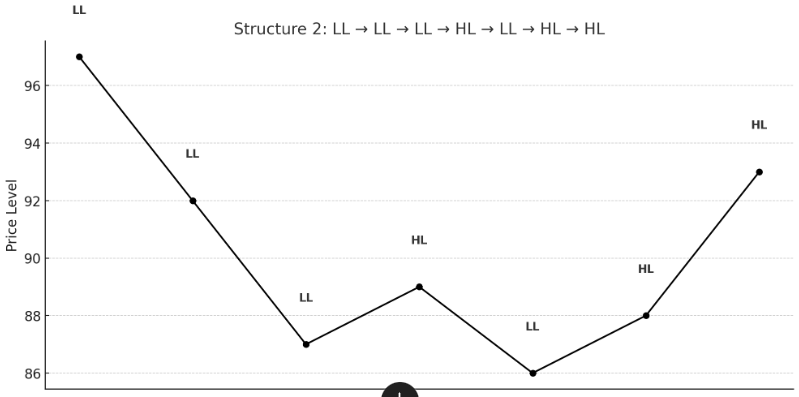
LL → LL → LL → HL → LL → HL → HL: The Grind Before the Genesis
This is where most traders get shredded. Not because they can’t see the lows. But because they keep expecting the bottom to stick.
The triple LLs are soul erosion. Every bounce is a betrayal. Every green candle is a setup for pain.
Then a higher low. It doesn’t mean much. Yet.
Another LL. But something’s different. It’s shallow. Weak. Unconvincing.
Then HL. Then another HL. Now we’re cooking.
Structural label: Death Spiral → Shallow Push → Reclamation Phase → Trend Genesis.
Enter Marcus Aurelius: “The impediment to action advances action. What stands in the way becomes the way.”
Exactly. That shallow LL? That was the obstacle-turned-path.
Now, Watch SPX Dance to These Structures
- 1999–2003: HL → LL → HL setup post-dot-com. The second HL in 2003 marked the real bottom.
- 2007–2009: LL → LL → LL → HL → LL → HL → HL. Textbook. The 2009 HL was the pivot.
- 2015–2016: Flush pattern. The HL that followed the China sell-off was where the engine reloaded.
- 2020: Pandemic low? LL to HL in hyper-compressed time.
- 2022–2023: Similar script. Panic, base, reclaim.
The patterns aren’t perfect, but they rhyme. Because they aren’t mechanical, they’re psychological.
So What Do You Do With This?
You don’t predict. You don’t react. You read.
You read pressure. You read reversal not as shape but as intention. This is a structure—alive, deceptive, recursive. The market speaks in sequence, not shouts. Forget the headline. Watch the build.
1. Track Sequence, Not Just Position
A single higher low? Irrelevant. Noise.
But a second HL after a shallow LL? That’s not just price—it’s resistance fatigue. It’s belief turning, slowly, into conviction.
You’re not looking for proof. You’re looking for a pattern. The market never declares. It infers. Your job is to catch the second inflection—where decay stutters and rebirth tries to crawl out.
2. Observe Energy, Not Just Price
Candles lie. Momentum doesn’t.
Use volume. RSI. MFI. But don’t just scan numbers—feel the pulse. Was the reclaim dry and desperate? Or did it punch through like it remembered what it used to be?
Energy reveals intent. Not in the spike—but in the rhythm. Don’t just watch movement—watch how it moves through time.
3. Assign Labels to Structural Events
Language creates recognition. Name the invisible.
- Flush — The final low that guts the late chasers.
- Anchor — The HL that holds when the crowd no longer believes.
- Drift — The sideways haze where both bulls and bears get baited into bad trades.
You’re not labelling the price. You’re labelling psychological events. Flashpoints in crowd memory.
4. Stay Narrative-Agnostic
Price isn’t prophecy. It’s friction. It’s mass emotion under constraint. The chart is not a statement—it’s a struggle.
Don’t chase what the crowd says. Track what it does under stress. Watch where hands shake. Watch where time compresses. That’s where truth leaks out.
The Deeper Logic: Sequence Over Shape
A V-bottom is nothing. A short squeeze is forgettable. But a V-bottom followed by an HL? Now we’re talking reflexivity. Structural memory. Systemic rebound.
Because charts aren’t about geometry—they’re about psychology, trying to rebuild trust.
Let’s zoom out.
There was a man once who tracked empires, not equities. He watched how they rose on shared belief, peaked in excess, and decayed in softness. Unless—unless—new energy emerged from the periphery.
Markets mimic this. LLs are decay. HLs are fresh blood. When a flush hits and a true HL holds, you’re not watching price action—you’re watching reformation.
The wise don’t chase rallies. They hunt structure. Because that’s what the market is—a living organism rebuilding itself in front of your eyes.
Final Notes: Want to Build a Structural Lexicon?
Language clarifies intuition. Here’s your shorthand:
- L3-HL2 — Third lower low, followed by second higher low.
- F2-A1 — Second flush, first anchor.
Mark them. Track them. These aren’t just setups. Their sentences are in the market’s ongoing novel. If you learn to read them—not as traders, but as strategists, poets, emperors—you stop chasing.
You start composing.
Because higher highs and higher lows aren’t “signals.” They’re narrative tension made visible. They’re the market trying to write itself out of chaos.
So read well. Move early.
Game on.
Unlocking the Hidden Forces Behind the Market